The possibilities offered by Meterpreter when developing post-exploitation modules are practically limitless. See for example the modules Imager.rb and NBDServer.rb developed by R. Wesley McGrew and presented at Defcon 19 under the title "Covert Post-Exploitation Forensics With Metasploit".
Such modules allow you to make a copy of physical volumes and logical drives on the compromised computer through the network; or mount the file system of those units on the attacker's computer as if they were another device. Not to mention the possibilities from the forensic standpoint that offer this kind of modules.
Much of this flexibility to carry all kind of tasks from a Meterpreter shell is offered by Railgun. This extension allows us to load Windows libraries in runtime and make use of its functions to have full access to the entire Windows API.
As a contribution to the list of post exploitation forensics modules I have developed a module to recover deleted files from NTFS file systems. In this way we can get not only "existing" files on the compromised computer but the "deleted" ones too (sometimes the most interesting).
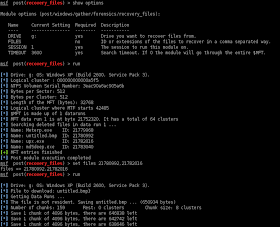
The idea of the module is to go through the entries of the $MFT (Master File Table) and list the deleted files. As the files are shown, it will add an ID associated with that file, which represent the offset of the MFT entry of that file on disk (the number of logical bytes from which that entry is located). If you want to retrieve a particular file you have to specify the variable FILES with that ID. Thus the module could read the corresponding entry to extract each of the dataruns associated with that file. If the file is resident its content will be extracted from the $MFT itself. Here's an example of its use:
As we see, if we do not specify the variable FILES, the module will list only deleted files. Later, to retrieve the desired files we have to specify their IDs in a comma separated way.
Another option to get files without specifying its ID is by extension. If we are interested only in certain types of files we can specify the desired extensions using the variable FILES. See the following example:
Keep in mind that the module extracts the content of each of the clusters associated with the file. Since the file is removed, its content may have been totally or partially overwritten, so It's likely that we get a corrupted file (which may be of interest also from a forensic standpoint).
It is also important to note that the process of listing deleted files on a large hard disk (with many entries in the MFT) can be extremely slow, in my tests about 8-10 entries per second. Because of this, with the variable TIMEOUT you can specify the number of seconds to invest in the search process.
Here I leave a How to video:


It's stunning the types and numbers of modules of meterpreter, great job for the comunity...
ReplyDeleteExtend this module to Linux is a good idea.
Again, thanks for the contribution.
You gained a follower!
P.S: I read the post's about shellcoding and its fucking great!